A New Era of Privacy
Tunnel is a patent-pending Faraday enclosure that allows you to conceal your location, protect your personal information, and evade unwanted surveillance. Tunnel gives you the ability to plan, move, and act without worrying about who’s keeping tabs on you.

A New Era of Privacy
Tunnel is a specially engineered phone case that lets you hide your location, escape surveillance systems, and protect your personal data. Tunnel gives you the freedom to plan, move, and act in total secrecy.
1. Insert your phone.
Place your phone inside your tunnel and fasten the cover.
2. Wait 8-10 seconds.
The average time it takes for any remaining EMF to be blocked.
3. You’re now untraceable.
You’re off the grid and free to go about your daily activities without being monitored.
Tunnel can be used with any mobile device.


$59.99
Only $41 when you order now.
Made in the USA. 100% satisfaction guaranteed or your money back.

What Others Are Saying
Features
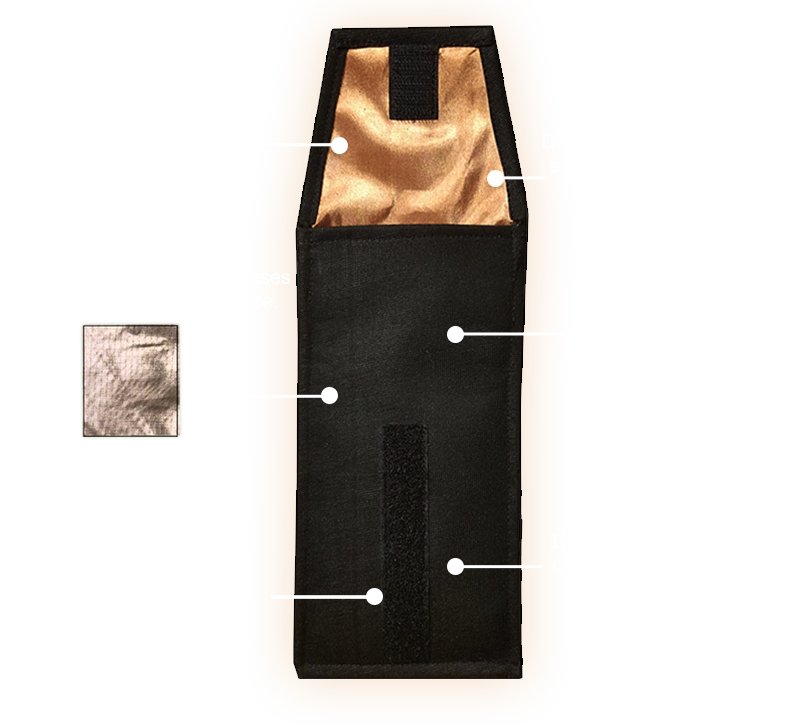
Features
Try it yourself. Risk free. 100% guaranteed.
We guarantee 100% satisfaction with your order, so you can try Tunnel for 30 days on us without risking anything. We know that once you experience the benefits, you won’t go back to being unprotected. If for any reason you’re unsatisfied with your purchase, simply send your Tunnel back to us within 30 days in the condition it was received and we’ll give you your money back — no questions asked. You’ve really got nothing to lose, and everything to gain.

Proven.
Constructed with 100% authentic copper — the same kind of metal used by agencies and industry specialists to hide their activity.
Powerful.
Your Tunnel uses a new patent-pending dual-layer compounding system with authentic copper plus an auxiliary nickel conductor to create an impenetrable shield.
Efficient.
Take Tunnel with you on-the-go, insert your device at any moment, and vanish in a matter of seconds.
Our Approach to Security
Even when you put your phone in airplane mode or switch it off, it can still function in a low-power state (baseband) and uses EMF. Bad actors can still track your “off” phone and monitor your location, activate your mic or camera, and see what you’re doing.
Surveillance regimes, malicious hackers, behavioral advertisers, analytics companies, social media sites, and many others have the ability to track you via your phone. After a decade of rigorous testing, we developed Tunnel so that you can completely block unwanted surveillance, misdirect prying eyes, and take action without others keeping tabs on you.

A Few Ways You Can Use Your Tunnel
- Conceal your location when engaging in secret activity.
. - Trick surveillance systems by appearing in unpredictable locations.
. - Disrupt attempts by others to track you or observe your patterns.
. - Give Tunnels to your friends and family to increase their security.
. - Prevent stalkers from prying into your personal photos and text messages.
- Give Tunnels to employees to use during sensitive company meetings.
.
- Guard your banking and financial information.
.
- Block criminal attempts at identity theft.
. - Prevent others from remotely activating your microphone and camera.
. - Hide your plans during politically sensitive operations.
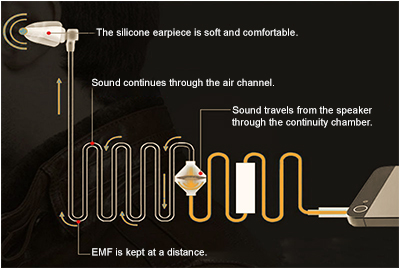
Order now and receive our anti-EMF covert earpeace with your Tunnel.
- Engineered with non-conductive air ducts which facilitate sounds, thus keeping you at a longer distance from EMF.
. - Compatible with all 3.5mm mobile device jacks for headphones.
. - Includes a microphone for two-way communication.
. - Equipped with an answer control button to conveniently accept calls.
$21.99
Free when you place your Tunnel order now.

Here’s What You’re Getting

Tunnel Case: $59
Earpiece: $21.99
Total value: $89.99
Order now for only $41.

If You Order Now
- + $59.99 $41: Tunnel Case
- + $21.99 Covert Anti-EMF Earpiece
Normal Value
- $59.99: Tunnel Case
- $21.99: Covert Anti-EMF Earpiece
It’s time to start defending yourself.
“Intelligence agencies and police are able to silently and secretly intercept calls without the help or knowledge of telecommunication providers. A user’s physical location can be tracked if they carry a smartphone, even if it’s on standby.”
“The location pings associated with each cell phone revealed work and life patterns. This enabled the researchers to determine the location of a user’s site of employment, the user’s home, and other places the user frequents. Once the address of a home was located, public records for the home were accessed to provide the name of the person and often the name of his or her spouse or other persons occupying the property.
The NSA has built an infrastructure that allows it to intercept almost everything. If I wanted to look into your wife’s phone, all I’d have to do is use intercepts. I could see her texts, photos, passwords, emails, credit cards, etc.
“You have not had any privacy since the first day you owned your first cell phone. They can track everything. They can hear recordings of anything you have ever said on your cell. And read everything you ever read, and everything you ever typed. And see every location you’ve ever been to. That’s just how cells work. Your privacy is a willful illusion.”
“Unless you live deep under the sea, you are probably well aware that large amounts of personal data are constantly being harvested. However, you may not be as aware of the many complicated ways that data is collected, nor what happens to it all afterward…These systems can know what you eat, who you vote for, what you like to watch, who you have relationships with and much more. “
“People don’t really realize that their mobile phone, with access to all these sensors, is, in some sense, potentially like the best spying device you can imagine…”
Frequently Asked Questions
Will my phone still work when I take it out of my Tunnel?
Yes. When you place it inside your Tunnel, the EMF is blocked and so your phone cannot send signals out. But as soon as your phone is taken out, it functions normally again. You can then retrieve messages that were left while it was Tunneled. Tunnel gives you the option to control when you are exposed or shielded. None of your data is harmed and the inner copper contains pliable polyester sheets which are gentle on phones.
Will my alarm and other apps function inside my Tunnel?
Yes. You can leave your phone inside your Tunnel when you sleep and the alarm will still work. Any app that does not need an external dependency on EMF will still work while Tunneled. For example, you can keep your headphone cord attached to your phone and pull the cover over it. This allows you to listen to any music you’ve stored on your phone while it’s Tunneled.
What if someone needs to call me in an emergency, can I still receive their calls?
Yes, as long as you keep your Tunnel cover partially open. This will allow just enough EMF inside for the call to connect, without exposing you to the EMF. Most people keep their phones partially Tunneled while they sleep at night. This way, they can be available for emergencies while directing the EMF directly to the phone and away from them.
I have a large phone, will it fit inside my Tunnel?
Yes! Tunnel can fit virtually all other phone sizes. If you have an unusually large phone with a bulky case that can’t fit inside, just send your Tunnel back to us for an exchange with one of our extra large sizes — but this is a rare circumstance since most phones will fit in the default size even with cases on.